Modern Challenges in Conducting OSINT Safely
Analysts across threat intelligence, fraud, and trust & safety teams need to:
- Visit risky or hostile sites without infecting their systems
- Access content as if they were in another country or region
- Conduct research without revealing who they are or what organization they work for
- Ensure no evidence of their activity persists after the investigation is complete
Traditional tools only solve part of the problem:
- VPNs and Tor hide your network location, but they don’t prevent tracking through browser, device, or behavioral fingerprinting
- Incognito or “privacy” modes offer limited protection and leave behind artifacts that can still be correlated to a user or organization
- DIY virtual machines and “cold” laptops are complex and expensive to manage at scale, and often leave residual data that can be recovered or attributed
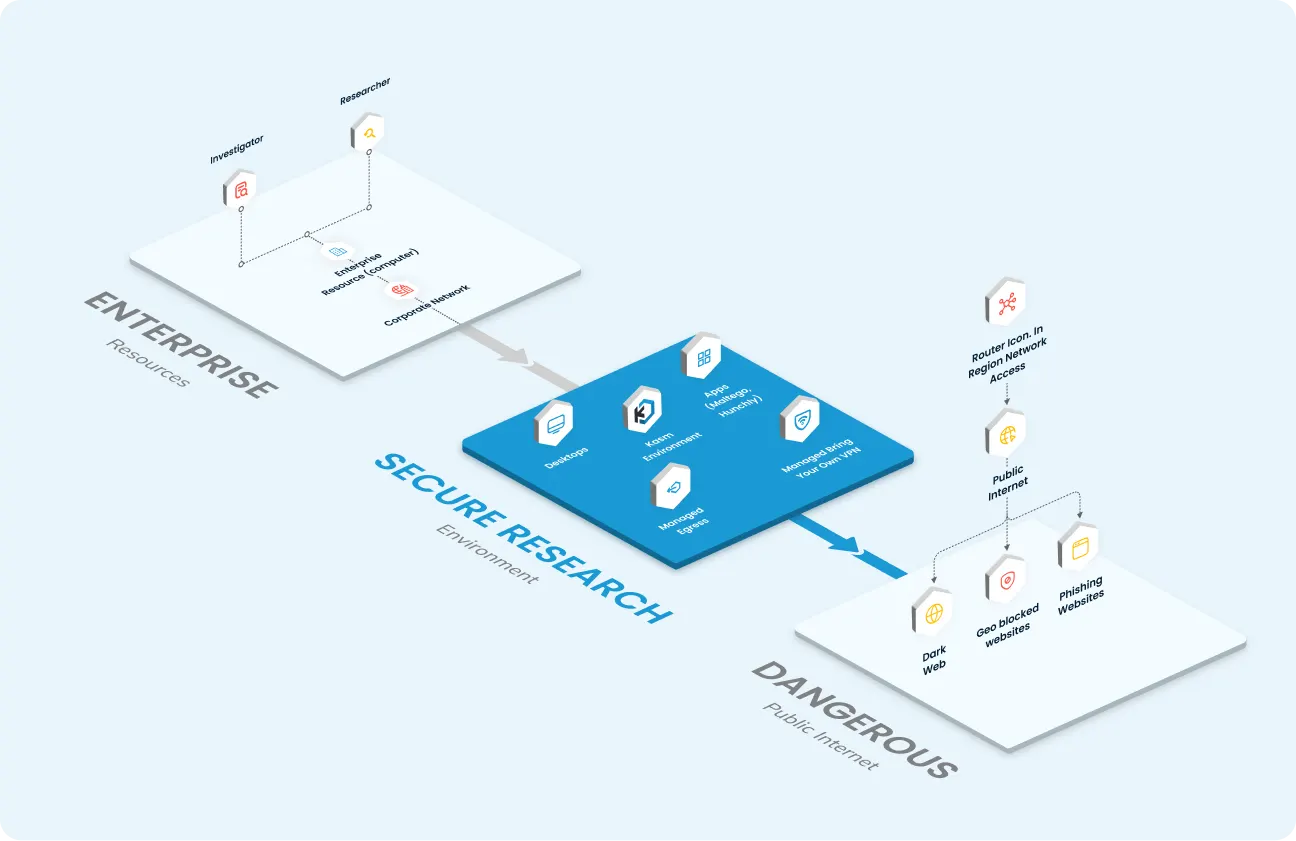
Kasm delivers a managed attribution platform purpose-built for secure web research. Analysts operate in disposable, isolated environments that leave no trace behind once destroyed, allowing teams to safely go online, collect what they need, and remain anonymous throughout the entire investigation lifecycle.
Experience the Web Without Exposing Your Identity
Kasm Workspaces is a Zero Trust Web Intermediary where all web interactivity runs inside disposable containers in anonymous cloud environments.
You interact with a live stream of the session, not the web itself:
You authenticate to Kasm Workspaces
A fresh containerized browser or desktop is created in a selected region or egress point
All interaction with surface or dark web resources happens inside that isolated container
Only pixels (visual output) are streamed back to your device; no active web code ever executes locally
When you’re done, the environment is destroyed, eliminating any artifacts or identifiers
Web Research Demo
Key Benefits for Digital Investigations
Private & Non-Attributable
- Browser workloads run from a global network of cloud points of presence
- Choose regional egress to approximate local user behavior and bypass georestricted content where policy allows
- Attributions and artifacts never tie back to your corporate network or analyst device
Zero Trust Isolation
- No agents or software required; sessions are accessed through a standard browser
- All content is contained within the remote container; nothing is stored or executed on your endpoint
- Malicious sites, drive-by downloads, and exploits are contained and discarded at the end of the session
Disposable by Design
- Every session runs in a temporary, single-use environment
- Once closed, the container and its data are destroyed, preventing fingerprinting, tracking persistence, and cross-session leakage
Full-Featured Research Environments
- Use current, full versions of leading browsers and Linux or Windows desktops
- Support for extensions, plug-ins, and investigation tools so analysts can work the way they want
- Optional Tor and dark web-capable workspaces for investigations that require it
Built for Threat Intel, CTI, and Investigations Teams
Kasm focuses on organizational size and maturity, not just industry. Typical users include:
For large enterprises, one organization may have multiple teams independently using Kasm Workspaces while benefiting from a common secure research platform.
Move Beyond DIY VMs, VPNs, and Legacy Tools
Many teams come to Kasm from either DIY setups or legacy managed attribution vendors.

Replace DIY Complexity
Instead of managing your own cold laptops, hypervisors, VMs, and VPN chains, Kasm provides:
- One-click access to secure research workspaces
- Centralized policy controls and user management
- No need to maintain images, patch VMs, or operate your own VPN infrastructure

Modern Managed Attribution
Kasm occupies the sweet spot between bare-bones browser streaming and ultra-premium bespoke attribution services:
- More flexible than basic RBI tools – full environments, dark web options, configurable egress, and tool integrations.
- More cost-effective than high-end, hyper-bespoke vendors –many investigations don’t require extreme, mobile or residential egress sourced through shell companies.
How Kasm Delivers Safe, Anonymous Investigation Sessions
User Authenticates
Analysts sign into Kasm via SSO or standard authentication, from any device with a browser.
Isolated Workspace Spins Up
A containerized browser or desktop launches in your chosen region or environment.
Secure, Anonymous Web Interaction
Analysts browse, log into sites, capture evidence, and interact with targets; all within the isolated environment.
Evidence Collection & Storage
Use built-in features such as screenshots and screen recording and connect to your cloud storage to store artifacts as needed.
Session Destruction
When the session ends, the container is destroyed, removing all local artifacts and preventing re-use of fingerprints or identifiers.
Tools & Integrations for Investigators
Digital investigations rarely happen in a browser alone. Kasm Workspaces is designed to bring your own tools:

- Investigation Tools Run OSINT tooling, such as Hunchly, within your Kasm Workspaces for structured evidence capture and link analysis
- Cloud Storage Connect to your organization’s cloud storage to securely store screenshots, recordings, exports, and case files
- Security & Identity Stack Integrate with your existing SSO, logging, and security platforms for streamlined access and governance
For teams with advanced or highly bespoke needs, Kasm also works alongside specialized digital investigation and managed attribution partners to create tailored solutions. Review our Integration Partners.

Enabling Secure Collections
Kasm gives intelligence and research teams what they need most:
- More flexible than basic RBI tools – full environments, dark web options, configurable egress, and tool integrations.
- More cost-effective than high-end, hyper-bespoke vendors –many investigations don’t require extreme, mobile or residential egress sourced through shell companies.
Industry Applications

Education
Enable faculty, researchers, and campus security teams to safely investigate online threats, academic fraud, and extremist content without exposing personal identities, student networks, or institutional infrastructure.
Learn More
Healthcare
Investigate healthcare fraud, counterfeit pharmaceuticals, data leaks, and public health threats across open and dark web sources. Enable secure, non-attributable OSINT research into illicit marketplaces, threat actors, and misinformation while protecting patient data, organizational networks, and analyst identities.
Learn More
Retail & Manufacturing
Investigate counterfeit goods, gray market activity, supply chain fraud, and brand impersonation across marketplaces, forums, and social platforms using non-attributable research environments.
Learn More
Financial Services
Empower fraud, AML, and threat intelligence teams to conduct discreet investigations into mule networks, scam operations, and illicit financial activity while maintaining compliance and protecting analyst identities.
Learn More
Government, Defense & Intelligence
Conduct secure OSINT and digital investigations across surface, deep, and dark web environments with policy-controlled, non-attributable access suitable for sensitive or classified missions.
Learn More
Energy & Industrial Applications
Support intelligence gathering and threat research related to critical infrastructure, adversary narratives, and activist or nation-state activity without exposing operational networks or analyst identities.
Learn MoreExplore Other Kasm Use Cases
Kasm Insights
Get Started with Secure Web Research
Traditional tools were not designed for modern OSINT and digital investigations. Kasm Workspaces gives your analysts safe, anonymous, and fully isolated access to the web, without the overhead of DIY infrastructure or the cost of ultra-premium vendors.