
Safe and Secure Access isolated browsing for secure access.
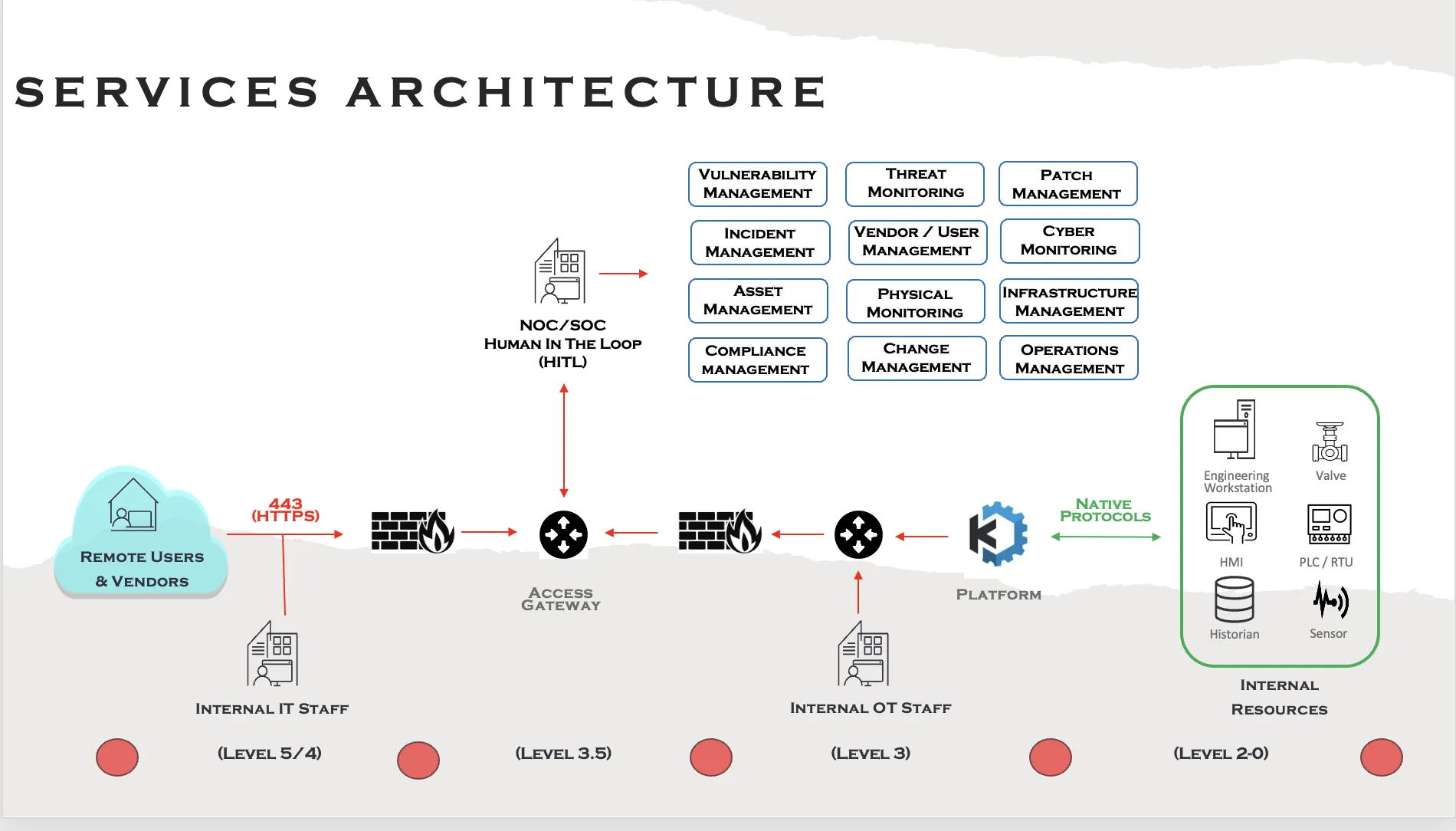
Give your Operational Technology teams real-time, context-driven cyber-physical visibility through a single pane of glass, enabling informed decisions without compromising security or control. Operators, vendors, & field engineers can access exactly what they need in seconds through isolated, disposable browser sessions, allowing secure Bring-Your-Own-Device (BYOD) and Bring-Your-Own-Applications while maintaining full isolation, auditability, & control.
Built for critical infrastructure environments, Kasm Workspaces delivers industrial-grade OT functionality while meeting regulatory, security, and IT-driven workflow requirements—enabling rapid response, reduced risk, and secure access at scale.
Gain visibility into your systems to reduce downtime and ensure safe operations
Industrial operations demand constant visibility to maintain operational safety, uptime and efficiency. Disconnected tools and blind spots increase operational risk, production loss, and exposure to negative regulatory, reputational and financial impacts.
Kasm is a cyber-physical operational access platform that unifies OT, IoT, cybersecurity tools, and enterprise systems into secure, governed workspaces. Instead of rip-and-replace or isolated point solutions, Kasm brings operational systems, data, and cyber context together under a unified platform of people, process and technology control.
This unified operational view gives teams the visibility and control they need to respond to incidents faster, collaborate securely, and restore operations safely—without unnecessary access or added complexity.
Functional OT & IoT Use Cases
Secure Managed Access
Secure Managed Access is more than just secure remote access for external users—it is a controlled, policy-driven access model for both external and internal users operating within OT, IoT, and industrial environments. Kasm provides secure, browser-based access to applications, devices, and operational systems without requiring changes to existing networks, protocols, or legacy infrastructure. Users are granted access through isolated, disposable workspaces that expose only approved resources, ensuring safety, operational stability, and compliance across all access scenarios.
Designed for environments where availability and safety take precedence, Kasm enables organizations to safely connect people to industrial systems without introducing unplanned changes, vendor lock-in, or security risk. Access is tightly governed, fully observable, and automatically revoked—supporting everything from five-minute view-only sessions to fully auditable maintenance workflows.
Key Benefits & Capabilities
Secure remote access for internal teams, vendors, and contractors—without VPNs or permanent tunnels
Granular control over user interactions with applications, devices, and industrial resources
Policy-driven access enforcement to ensure safety, security, and adherence to approved change processes
Disposable, isolated workspaces that expose only approved applications and views
Data loss prevention (DLP) controls, including read-only access and upload/download restrictions per user
Time-bound access controls (e.g., five-minute view-only sessions) that automatically expire
Full session recording and audit logs to maintain visibility into user actions
Native protocol support with no changes to existing OT protocols or workflows
No IP address changes, no network reconfiguration, and no application or device modifications required
Works over low-bandwidth connections through a standard browser with no software installed
Industrial-grade isolation ensures no data, scripts, or malware leave the controlled environment
Visibility into user activity and access across environments, down to industrial device levels
Incident Management
Incident Management is the structured lifecycle of preparation, detection, analysis, containment, eradication, recovery, and lessons learned used to respond to cyber, physical, and cyber-physical incidents. While IT and OT teams often follow similar response frameworks, the tools, workflows, and risks in OT environments are fundamentally different—where missteps can impact safety, availability, and evidence integrity.
Kasm is designed to support both IT and OT incident response needs within a single platform. It provides incident response teams with a secure, browser-based environment to coordinate response efforts, analyze threats, and contain incidents without introducing additional risk or relying on external cloud services.
The platform enables rapid control of incidents through a purpose-built incident command and collaboration center, integrated forensic and OSINT investigation tools, and a secure payload detonation environment. Teams can preload operational playbooks, diagrams, call lists, and critical response materials so they are immediately available during an incident—even if normal systems are inaccessible.
Kasm command centers can be quickly deployed within an environment or spun up on demand, allowing teams to coordinate response efforts securely. Responders, including trusted third parties, can join through secure session invitations without requiring network changes or exposing sensitive data outside the organization.
Designed for degraded and disconnected environments, Kasm continues to operate over low-bandwidth links and minimal compute resources. This enables effective incident response across remote and constrained locations such as offshore platforms, mines, maritime operations, DER sites, and monitoring stations.
Kasm functions as a portable, self-contained Incident Response “go bag,” providing teams with the tools and visibility they need—when and where they need them most.
Key Benefits & Capabilities
Secure, browser-based incident command center for OT and cyber-physical incidents
Rapid spin-up of isolated Kasm environments during outages or active attacks
Secure casting links to bring responders into the command center without network changes
Built-in OSINT desktops and investigation tools to support rapid analysis
Centralized collaboration for security, operations, engineering, and leadership teams
Full session recording and timestamping for compliance and post-incident review
Isolation of response activities to preserve operational safety and evidence integrity
Alignment with established incident response frameworks and workflows
Faster containment and recovery to reduce blast radius and restore operations
Threat & Patch Management
Threat & Patch Management is a human-in-the-loop (HITL) controlled process that enables organizations to identify, assess, prioritize, mitigate, and remediate cyber and physical risks across OT, IoT, and industrial environments. It supports secure vulnerability management without disrupting operations, introducing unapproved changes, or compromising system availability and safety.
Kasm enables organizations to integrate their existing threat detection and assessment tools while using the Kasm platform to safely contain threat analysis, mitigation, and patching activities. All remediation actions are performed through isolated, disposable workspaces that enforce strict access controls, full observability, and auditable change management—ensuring operational stability throughout the remediation lifecycle.
Key Benefits & Capabilities
Secure assessment and remediation of threats across OT, IoT, and industrial environments
Integration with existing threat detection, identification, and risk assessment tools
Isolated, disposable workspaces for threat analysis, patch testing, and remediation
Compensating controls (supervised access, session recording, DLP, access restrictions) applied while patches are pending
Policy-driven change control to ensure remediation occurs only during approved maintenance windows
Secure download, staging, and deployment of patches through enforced DLP controls
Built-in CI/CD pipelining and infrastructure orchestration for controlled patch deployment
Full session recording, timestamping, and audit logs for all remediation activities
Safe sandboxing for malware scanning, forensic analysis, and patch validation
Support for patching and updating industrial assets, including PLCs, HMIs, RTUs, and OT applications
Centralized, secure patch repositories accessible without banned physical media or untrusted downloads
Automatic workspace teardown after remediation to eliminate persistence and residual risk
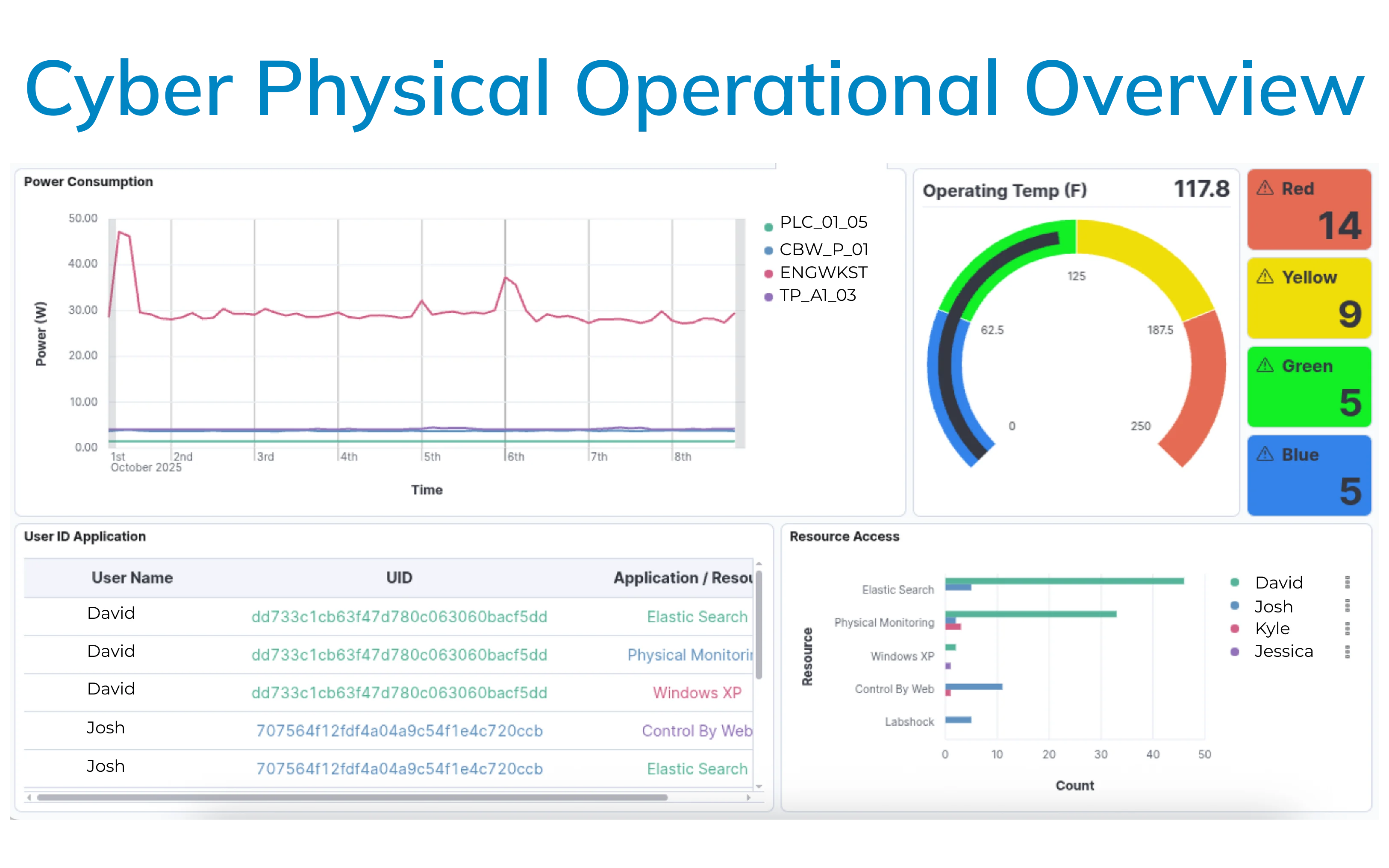
Cyber Physical
Critical Infrastructure organizations can’t afford to have disconnected tools, processes or remote operations giving them blind spots in their infrastructure. And while some organizations have SIEM and SOAR tools, these and predominantly IT focused and lack critical OT context.
Teams need real-time visibility into what’s actually happening across their infrastructure. It requires a managed platform that brings together their cyber and physical systems, data, and actions into a unified 360 Degree operational view of their environment.
Having this Operational View of their Cyber-physical systems (CPS) from PERA Levels 3-0 (computing systems, network resources , industrial systems, sensors, operational processes, etc.), their data and their users actions gives organizations the who, what, when, where and how heartbeat of they need today.
This heartbeat not only gives them the operational status and context they need to be safe and secure, but it also improves their operational uptime, their mean-time values (MTTR, MTBF, MTTF), overall operational efficiency and allows them to quickly respond to any cyber or physical incident with actionable intelligence.
From a business perspective it can reduce operational costs, increase profits, improve operational efficiency (OE), reduce maintenance calls / truck rolls and help them avoid costly incidents and events that can damage their reputation and increase regulatory scrutiny.
The Kasm platform is designed to give teams the capability to build that single-pane of glass view of their most critical business operations. Instead of forcing rip-and-replace or locking you into a rigid product, Kasm integrates your existing OT, IoT, cybersecurity tools, internal systems, and third-party products into secure unified workspaces allowing them to safely and securely live side-by-side under one set of policies, tailored to how your teams work, collaborate and respond.
Examples of industrial and environmental indicators, include:
Door sensors and access controls
Motion monitors and motion-triggered alarms
Rail and track integrity sensors
Cabinet and enclosure sensors
System monitoring and alerting platforms
Environmental sensors, including temperature probes
The Growing Need for Safe, Immediate OT & IoT Access
OT/IoT environments sit where cybersecurity, physical safety, and uptime collide. The stakes are higher, the systems are older, and the access demands are relentless. Teams are under pressure from:

Global vendors, contractors, and remote staff need fast access during outages or break-fix events but permanent tunnels and unmanaged endpoints increase exposure.
Safety-Critical Access Requirements
Operational Complexity and Distributed Teams
Legacy OT That Wasn't Built for Modern Connectivity Methods
Rising Compliance, Regulatory and Audit Requirements
Kasm meets these realities by acting as the secure access platform between people and operational systems — enabling speed and safety without opening OT networks to unnecessary risk.
Experience OT/IoT Access Without the Risk
Kasm streams desktops, apps, and industrial dashboards through isolated browser sessions. OT and IoT systems remain protected in their environment — never exposed to the user’s device, network, clipboard, or malware risk.
Teams get secure, just-in-time access that is fast, reliable, and auditable — without “winging it” through unsafe remote methods.
Key Platform Benefits for OT/IoT Teams

Built for OT, IoT & ICS Operations
Kasm enables secure, operationally aligned access across real industrial use cases:
Secure Remote Operations & Monitoring
Stream SCADA dashboards, HMIs, or IoT sensor analytics into isolated workspaces for engineers and operators.
Vendor & Contractor Access:
Grant limited, time-bound access without exposing internal networks or opening permanent tunnels.

Troubleshooting & Field Maintenance
Allow technicians to safely access OT environments from unmanaged or personal devices without contaminating production networks.
Incident Response & Training
Deliver safe workspaces for incident response, threat investigation, training and OT cyber readiness without touching live systems.
Compliance-Aligned Platform Capabilities
Kasm supports the implementation of controls required by these and more:
NERC CIP
ISA/IEC 62443
ISO 27001
NIST (800-82, 800-161, 800-53, CSF)
NIS 2 (EU) 2022/2555
CISA/NCSC
CIS Critical Security Controls
ASD/ACSC
BSI-CS 108
CMMC Level 2
Important Note:
Kasm provides platform capabilities that enable your organization’s regulatory requirements. Certification depends on how controls are implemented, managed, and maintained by your organization. Learn More
Core Platform Features for OT/IoT Access
Browser-Based Delivery
Only a browser is needed ideal for industrial sites with mixed or aging hardware.
Container Streaming & Automatic Disposal
Sessions launch instantly in secure containers and are destroyed on exit.
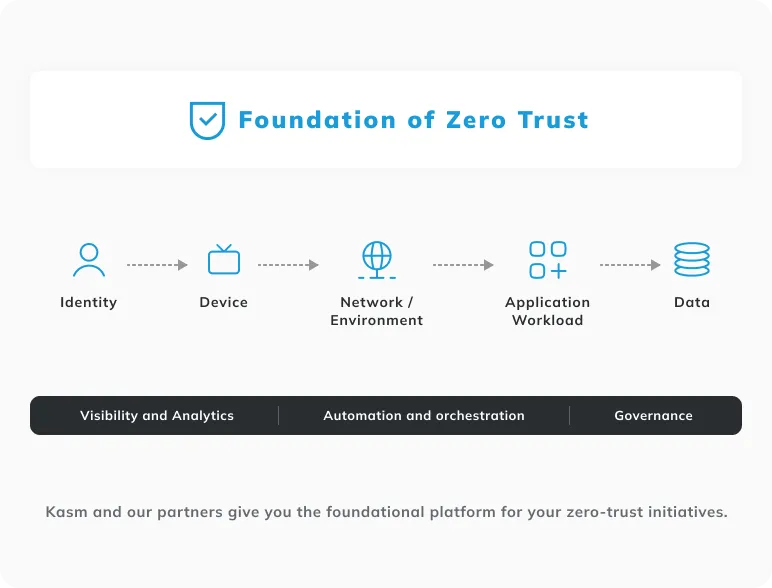
Zero-Trust Security by Design
Identity-based access, isolation by default, and no lateral movement.
Full Session Visibility & Auditability
Session recording and logs provide the traceability industrial compliance requires.
Scalable Architecture
Built on Docker/Kubernetes for on-prem, cloud, edge, or hybrid deployments.
How OT & IoT Teams Use Kasm
Just-In-Time Vendor Access
Temporary sessions for emergency maintenance without permanent network pathways.
Granular Operational Access (PLC, RTU, HMI)
Deliver controlled access to operational resources and applications without exposing backend networks.
Isolated Access for Field Engineers
Supports BYOD/BYOA without risking malware or data leakage.
Segregated Networks for Compliance
Ensure IT and OT never directly connect while still enabling safe access.
Unified Operational Workflow Execution
View data, issue tickets, communicate, and resolve incidents from one secure platform.
The Business Impact
Kasm Workspaces drives measurable OT/IoT outcomes:
- Reduced Cyber Risk through isolation and zero-trust enforcement
- Faster Response Times with immediate access provisioning
- Stronger Safety Posture via controlled, secure managed access
- Lower Cost & Complexity versus VDI, jump hosts, or VPN sprawl
- Improved Compliance Readiness with audit logs and session recording
- Extended Legacy System Lifecycles by offloading access workloads to containers
- Modernization Without Disruption keep the workflows, secure the access
We Enable Our Partners to Deliver Always-On OT/ICS Security and Operations
We enable our partners and clients to deliver 24×7×365 support across all facets of their OT/ICS infrastructure. Our platform is purpose-built for mission-critical environments, providing the visibility, access, and control required to safely operate, secure, and respond across complex industrial systems.
Through a single, unified platform, partners can provide:
- Continuous 24×7×365 Operational Support
- 360° Real-Time Operational Visibility
- A Zero Trust Network Access Foundation for OT/ICS
- Provide tools for threat management and mitigation
- Continuous Integration & Continuous Development application management
Our Strategic Partners
We work closely with industry-leading partners to extend the reach of our platform and deliver expert-driven operational, security, and engineering outcomes across OT/ICS environments.

GuidePoint Security
brings together proven expertise, great relationships, and leading technologies to solve our client’s most complex cybersecurity challenges. As a trusted cybersecurity advisor and partner with deep expertise across IT, OT, ICS, and critical infrastructure, GuidePoint keeps people, data, and operations safe. We deliver tailored cybersecurity services - from strategic consulting to implementation and incident response - that adapt to safeguard complex industrial environments today and provide complete confidence in their cybersecurity tomorrow.
By leveraging our platform, GuidePoint enables 24x7 operational support, real-time visibility, and rapid cyber-physical threat response for their OT/ICS clients.
Learn More
Barry-Wehmiller
is a global capital equipment and engineering solutions company serving manufacturing, packaging, and industrial markets. Known for its deep operational and engineering expertise, Barry-Wehmiller helps organizations design, build, and optimize safe, efficient, and resilient industrial systems.
Through our platform, Barry-Wehmiller enhances secure remote access, operational visibility, and Zero Trust foundations across OT/ICS environments—supporting both modernization and long-term operational excellence.
Learn MoreIndustries We Serve
Deploy the Kasm platform:
Modern Access for Critical Infrastructure
Secure, unified access to OT and IoT systems designed to improve visibility, reduce risk, and accelerate response.



